Table of Contents
Create and Manage Security Groups
This manual provide a quick help on how to create or delete the security groups and their rules using Security Groups Dashboard.
To login:
Authenticate using: Keystone Credentials
Domain: gwdg
User Name: your academic email (e.g. myname@gwdg.de)
Password: your Password
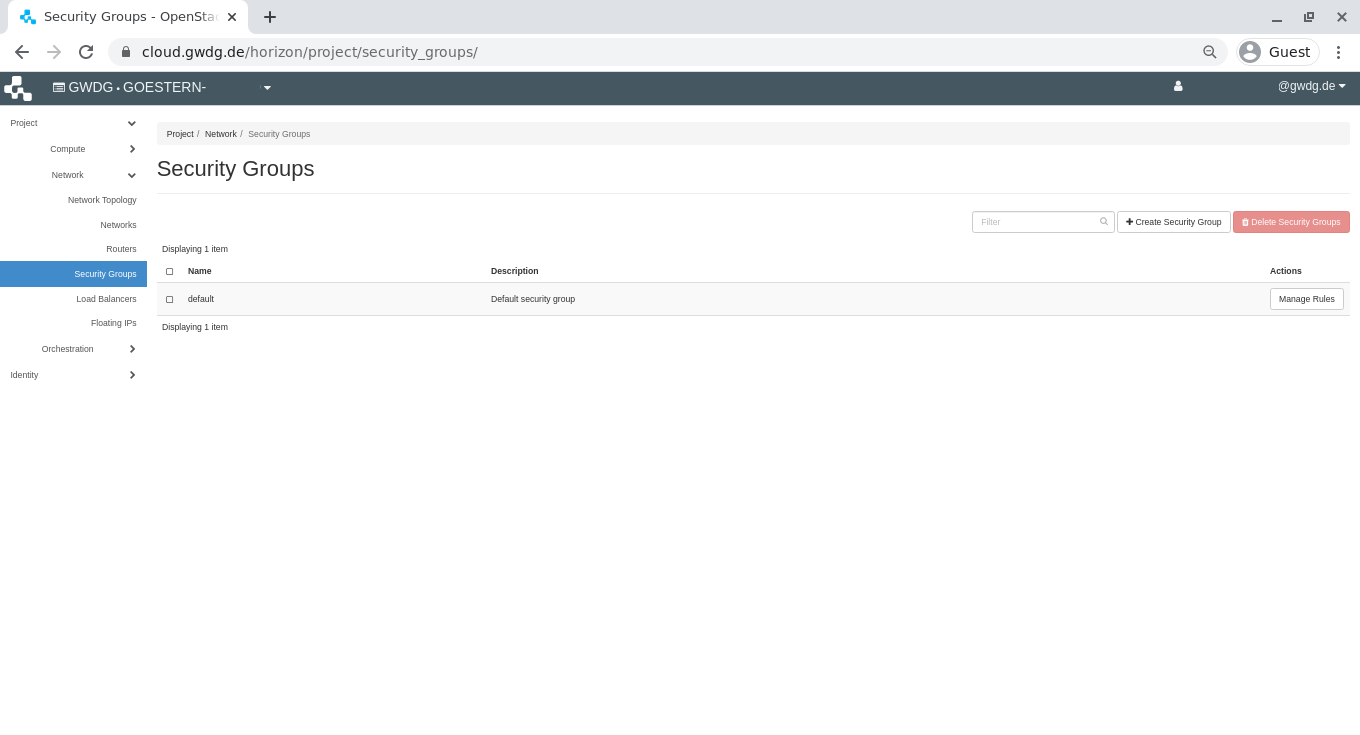
Manage Security Groups
You can create new security groups, in order to provide certain servers with specific access. They can be added to servers in the time of Create or Edit the server.
1- From the left menu bar, select Project→Network→Security Groups and then click “Create Security Group”.
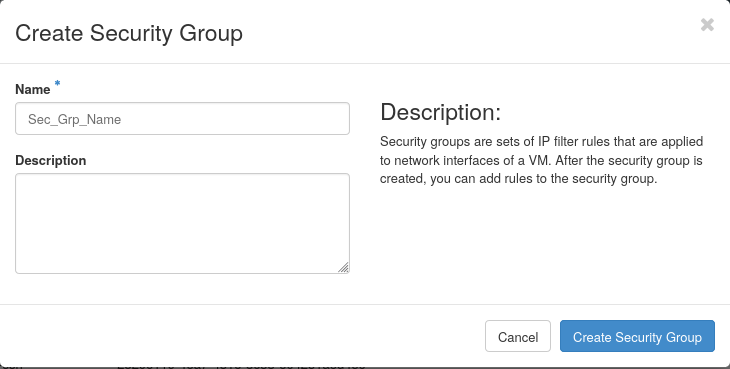
2- Determine a unique meaningful name and an optional description then click “Create Security Group”.
Manage Security Rules
You can add/remove security rules to/from a security group, in order to change the provided access. If the security group is already added to a server, the changes would be applied immediately.
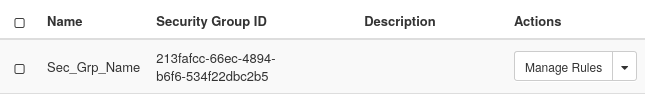
Click “Manage Rules” from the very right of the security group row.
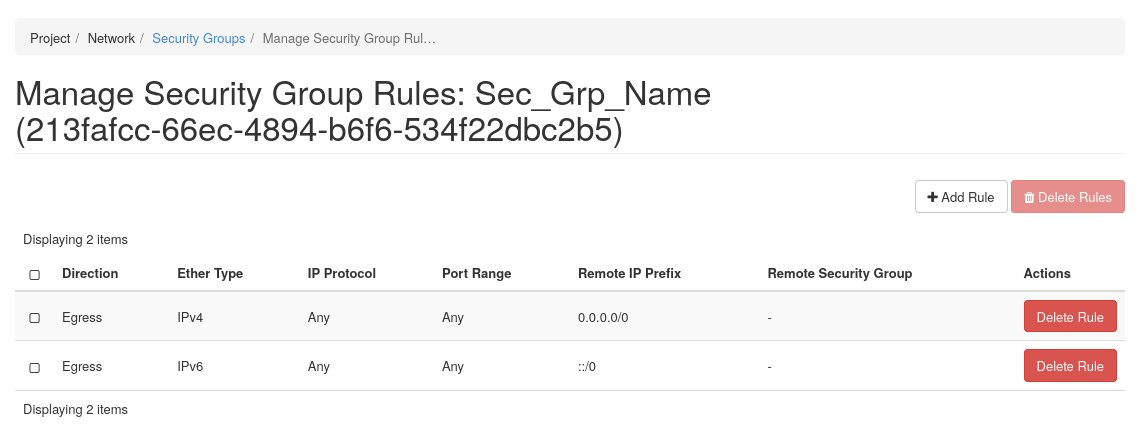
A form containing all defined rules will be shown. By default all ports are opened for outbound connections and no inbound connections are allowed. As a result, you can see that it contains 2 Egress rules whit no limitation on IPs and ports.
To add a new rule, click “Add Rule” on top-right of the form.
To define a rule, first select a protocol from “Rule” drop-down list (for example SSH), then fill its required field.
Leave the “Remote” field with the value CIDR, and in “CIDR” field specify the IP range from where you want to connect to your server. The default value “0.0.0.0/0” means from any IP (no protection).